Why Account Setup Deserves Careful Attention
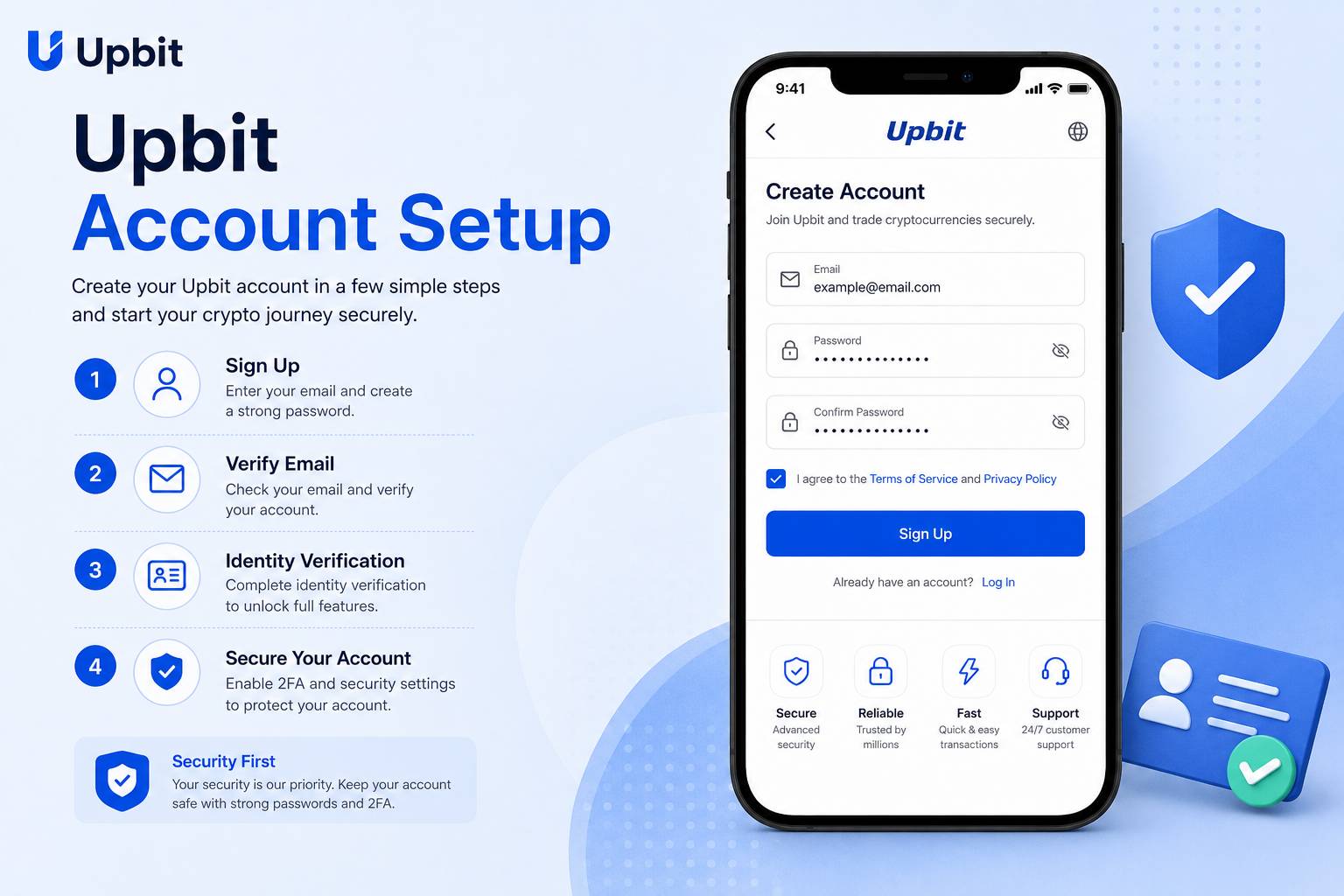
Account setup is the foundation of every crypto platform experience. Before a user explores market pages, mobile tools, trading features or asset sections, the account itself should be created and protected carefully. Many users search for Upbit because they want to understand the app experience, but the first important step is not a chart, a market list or a trading panel. The first important step is building a safe account environment.
A crypto account can include sensitive personal information, login credentials, identity-related steps, transaction records, security tools and access to digital assets. Because of this, account setup should not be treated like signing up for a casual website. A user should slow down, review each screen, understand what is being requested and confirm that the setup is taking place through a trusted app or website path.
Good setup habits reduce future problems. A strong password reduces unauthorized access risk. A protected email account helps secure recovery and notification channels. Authentication tools add another layer of protection. Trusted devices reduce exposure to malware and unknown sessions. Clear profile information can help avoid account confusion later. Each small step contributes to a stronger account structure.
This guide is written for English-speaking users who want a practical and calm explanation of account setup. It is not official platform support and does not provide account-specific instructions. Instead, it explains the mindset, preparation and safety habits that users should consider before and during the setup process.
Prepare First
Use a trusted device, secure email account and private connection before beginning any crypto account setup process.
Protect Access
Create a unique password, enable available authentication tools and keep recovery information private.
Review Carefully
Read account notices, verification prompts and security settings before moving into trading or asset features.
Prepare a Secure Email Account
The email account connected to a crypto platform is more important than many new users realize. Email may be used for account confirmation, login alerts, password reset messages, security notices and support communication. If the email account is weak, the crypto account may also become vulnerable. A user should prepare email security before creating or accessing a crypto account.
The email password should be strong and unique. It should not be reused from social media, shopping accounts, forums, cloud storage or other websites. Reused passwords create risk because a breach on one service can expose another. Attackers often test stolen email and password combinations across many platforms. A unique email password helps reduce this risk.
Authentication should be enabled on the email account when available. A second layer can help protect account recovery and login messages. Recovery options should also be reviewed. Old phone numbers, forgotten backup emails or weak recovery questions can create hidden problems. Users should make sure they control the recovery channels attached to their email.
Email habits matter as much as settings. Users should avoid clicking unexpected links that claim to be account setup messages, verification requests or urgent security notices. A safer approach is to open the app or website through a trusted source and check account messages from inside the platform. During setup, every email should be reviewed carefully before any link or button is used.
Choose a Trusted Device and Private Connection
Account setup should happen on a device the user controls. Public computers, borrowed phones, office machines, internet cafe terminals and shared devices should be avoided. A device used for crypto account setup may handle passwords, identity information, authentication prompts and account security settings. It should be clean, updated and private.
A trusted device should have a secure screen lock, updated operating system and reliable browser or app environment. Users should avoid devices with suspicious apps, unknown browser extensions, remote access tools or security warnings. A compromised device can capture passwords or alter information even when the user believes the website or app is legitimate.
A private connection is also important. Public Wi-Fi in hotels, airports, cafes or public spaces may be insecure. A fake network can imitate a real network name and collect user traffic. Account setup should ideally happen through a trusted home network or secure mobile data connection. Users should not upload identity information, create passwords or confirm security settings on unknown networks.
Physical privacy matters as well. Account setup screens may show personal information, verification codes, email addresses or security options. Users should avoid setting up accounts in crowded spaces where someone can watch the screen. A quiet private environment helps reduce mistakes and exposure.
Create a Strong Login Foundation
A strong login foundation begins with a unique password. A crypto account password should not be simple, reused or based on personal details. Names, birthdays, phone numbers, common words and predictable patterns are weak choices. A password should be long, difficult to guess and different from every other account.
A password manager can help users create and store unique passwords, but it must also be protected. Users should not store crypto account passwords in screenshots, plain text files, unsecured notes, messaging apps or shared cloud folders. A password is only useful when it remains private.
Users should also think about what happens after password creation. They should review whether authentication is available, whether login alerts can be enabled and whether account recovery options are clear. A strong password is the first layer, not the entire security plan.
Setup checklist
- Use a secure email account.
- Start from a trusted device.
- Avoid public Wi-Fi during setup.
- Create a unique password.
- Enable available authentication tools.
- Review all account notices carefully.
Understand Verification and Account Status
Crypto platforms may require verification steps depending on region, account type, available features and legal requirements. Verification can involve confirming email, phone, identity details or other account information. Users should understand that verification is not just a formality. It may affect account access, feature availability, limits or security recovery.
Verification should only be completed through trusted platform paths. Users should not submit documents through random links, direct messages, social media accounts or unofficial support chats. Fake verification pages are a common risk because they can collect sensitive documents and account details. If a verification request arrives unexpectedly, the user should open the app or website directly from a trusted source and check from inside the account area.
Users should read verification instructions carefully. Information should be accurate and consistent. Documents, names, dates and account details should not be entered casually. Mistakes during setup can create delays or future account issues. A careful user reviews before submitting rather than trying to correct errors later.
Account status should also be checked after setup. Users should know whether the account is fully active, whether verification is pending, whether any restrictions apply and whether security settings need attention. Understanding account status helps users avoid confusion when certain features are not immediately available.
Enable Security Features Early
Security features should be reviewed immediately after account creation. New users sometimes skip security because they want to explore markets first, but this is a mistake. The account should be protected before it becomes active. Authentication tools, login alerts, device management and withdrawal protections may be available depending on platform settings. Users should review each option and understand its purpose.
Authentication tools can reduce the risk of unauthorized access. They may require a code, device confirmation or other approval beyond a password. Users should never share authentication codes with anyone. A real support process should not require a user to reveal one-time codes or private recovery information. Any request for those details should be treated as suspicious.
Login alerts can help users notice unexpected activity. Device review tools can help users see where the account has been accessed. Withdrawal protections can add caution before assets leave the account. These tools may feel like extra steps, but they exist to protect the user. A few extra seconds during setup can prevent serious problems later.
Users should also record recovery procedures safely. They should understand how to recover access if a phone is lost or an authentication method changes. Recovery information should be stored privately and not shared through screenshots, chat messages or unsecured cloud folders.
Review Account Settings Before Using Advanced Features
Once the basic account exists, users should review settings before moving into trading or asset transfers. Account settings may include profile details, notification preferences, security controls, language options, device history and support information. Understanding these sections helps users know where to return if something needs attention later.
Notification settings deserve careful review. Too many alerts can create noise, while too few alerts can cause users to miss important account activity. Users may want security alerts, login notifications, transaction notices or market alerts depending on their habits. The best setup depends on the user, but the user should intentionally choose settings rather than ignore them.
Users should also check whether account messages or notices are available inside the app. Important updates may relate to features, security, supported assets, fees or platform rules. Reading notices is part of responsible account management. A user who ignores account messages may miss important changes.
Profile information should be reviewed for accuracy. Email, phone, region and identity-related details may affect account access or recovery. If information is outdated, users should follow the correct platform process to update it. They should avoid using unofficial channels to change sensitive account details.
Common Account Setup Mistakes to Avoid
One common mistake is rushing. Users may try to create an account quickly because they want to view markets or use features immediately. Rushing leads to weak passwords, missed warnings, incorrect information and ignored security settings. Account setup should be handled calmly, not treated as an obstacle.
Another mistake is using an unsafe access path. Users may click an advertisement, message link or unknown search result without checking. Fake pages can look convincing. A user should begin setup only from a trusted app source or verified website path. If the page looks unusual or asks for unexpected information, the user should stop.
A third mistake is ignoring the connected email account. Even a well-protected crypto account can become vulnerable if the email account is weak. Email security should be prepared first, not after a problem appears. Users should protect email with a unique password and authentication tools where available.
A fourth mistake is storing sensitive information carelessly. Passwords, recovery details, identity documents and authentication backup information should not be kept in public notes, screenshots or chat threads. Sensitive information should be stored securely and privately.
Maintaining the Account After Setup
Account setup does not end after the first login. Users should maintain the account over time. This includes reviewing security settings, checking active devices, updating passwords when necessary, protecting email access and monitoring account notices. A crypto account should be treated as an ongoing responsibility.
Users should periodically review whether old devices still have access. A phone replacement, laptop sale or shared device can create lingering risk if sessions remain active. Where device management is available, unfamiliar sessions should be removed. Users should also be alert to login notifications that do not match their own activity.
Passwords and authentication settings should be reviewed after any suspicious event. This includes phishing messages, lost devices, email compromise, strange login prompts or unexpected account notices. Waiting can increase risk. A calm and immediate review from a trusted device is the best response.
A well-maintained account helps users approach platform features with more confidence. It does not remove market risk, but it reduces avoidable account risk. The strongest setup is not only technical. It is a routine built from careful preparation, safe access, security awareness and regular review.
Important Notice
This page is an independent educational account setup guide. It is not operated by or officially affiliated with Upbit. The content is provided for general information only and should not be considered financial, investment, legal, tax or account-specific advice. Users are responsible for personal account security and platform activity.